About
Events and Activities
Highlights
Collaborations
Publications
Our Team
Goals and Objectives
About
The center carries research in information security to help governmental organizations and local institutions to protect their information infrastructure from cyber attacks. More specifically, the center will work with organizations to identify threats, quantify risks, and take remediation measures to mitigate the effect of possible cyber attacks. The center also can work with organizations to implement security standards and achieve compliance with the highest industry and government regulations.
Events and Activities
-
Workshop on SudoRange and SudoCyber
-
Seminar on Robot Control and Security
Highlights
1. Spatial Database Outsourcing in Cloud Computing

2. Social Networks

Nowadays, social network sites; such as Facebook and Twitter, have tremendous number of users in their repositories. Having this huge amount of data requires analyzing them to get statistics about the users and their interests. The information gained from mining social networks can be used in various applications such as recommendations, influence analysis and customer segmentation. The goal of the research group is to devise new techniques for extracting meaningful information inside today's social networks.
3. Wireless Sensor Networks
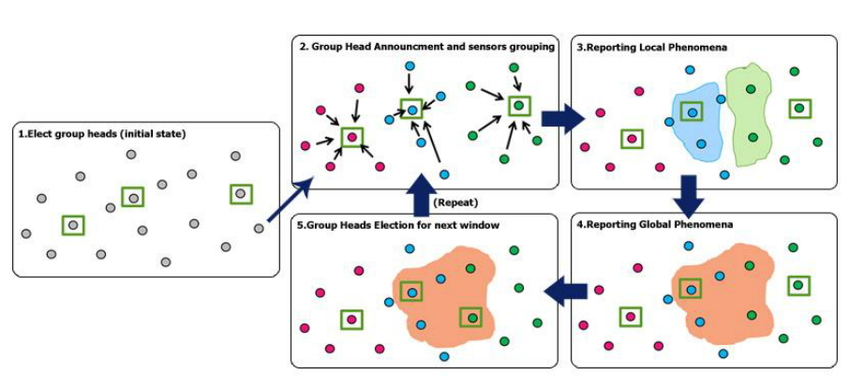
Wireless Sensor Networks (WSN) typically consists of a large number of small, low-cost sensor nodes distributed over a large area with possibly one, or more, powerful sink node gathering readings of sensor nodes. The sensor nodes are tiny devices equipped with one or more sensors, some processing circuits and a wireless transceiver. Each of these sensors gathers its own observation of the environment which can be used with other sensors' gathered data to provide a global view of the monitored environment to a user. Many applications are developed using WSN in the area of environmental and habitat monitoring, object and inventory tracking, health and medical monitoring, battlefield observation and industrial safety and control. In many of these applications, real-time data mining of sensor data to promptly make intelligent decisions is essential. Detecting phenomena in dynamic WSN environment where the sensors are mobile and data clusters are dynamic is a challenging problem.
4. Cyber Bullying in Social Networks

The popularity of social networks, such as Facebook, Twitter and Instagram, has dramatically increased during the last years, especially with the exponential growth in smartphones and mobile devices. Cyberbullying is an example of such threat impacting children, teenagers and young adults. It consists of posting aggressive and harassing messages, spreading rumors as well as sharing personal information, photographs and videos about the victims without their consent for the purpose of humiliating and making fun of them. Unfortunately, this threat is also becoming a significant issue in the UAE, especially with the wide adoption of Internet technologies and social media by UAE's population, mainly by the young generation. In this context, we aim in this research project at designing a framework for the detection and characterization of cyberbullying activities in online social networks. More precisely, we aim to identify relevant features and behaviors that characterize a cyberbullying threat and the involved users and design classifiers and algorithms to detect such threats.
5. GPS Spoofing Attacks in FANETs
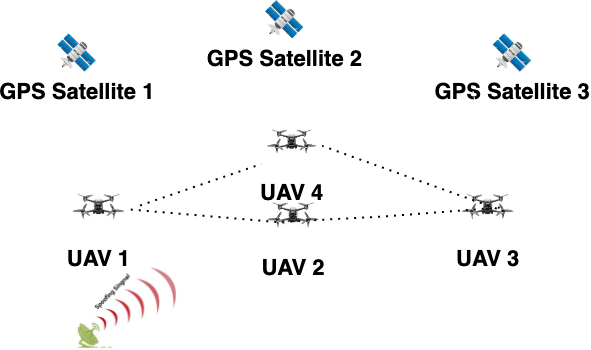
Flying Ad-hoc Network are group of Unmanned Ariel Vehicles (UAVs), popularly known as drones, connected in Ad-hoc manner to accomplish common missions. FANETs cannot impose algorithms requiring complex computations and storage due to the smaller size, lightweight, power and cost constraints of the drones forming the network. FANETs are becoming a target of various cyber-attacks as well. Drones rely on Global Positioning System (GPS) for its localization and the civilian GPS signals are unencrypted. It can be easily spoofed. Drones can be deviated from their path to attacker's indented destination by counterfeit GPS signals. The result of such attacks can be drastic; leading the UAVs to collide or hijack causing mission failures. This research aims to detect and mitigate GPS spoofing attack in FANETs using the information, that are exchanged among the drones in the FANET.
6. Security Attacks and Countermeasures in Opportunistic Mobile Networks
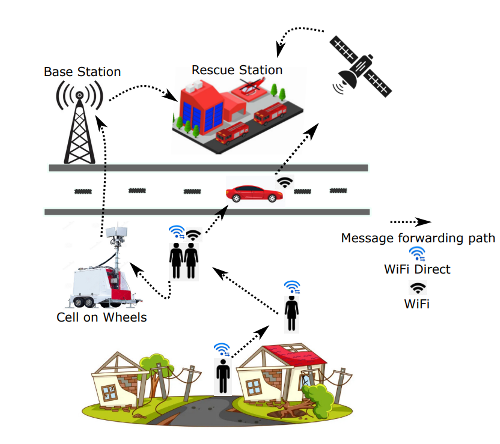
Opportunistic Mobile Networks (OMNs) is a network of opportunistically connected portable devices that can work in both infrastructure, and infrastructure-less environments. Conventional communication methods fail during disasters (i.e., earthquakes, floods, etc.), in crowded places (i.e., concerts, protests), or in areas having below average telecommunication resources (i.e., deserts, under-water, villages) when communication is more crucial. In this environment, the information is transferred over several nodes that transmit carried messages when come in transmission ranges of each other. OMNs are open network where nodes and as such they are vulnerable to cyber-attacks as compared to conventional (well-connected) networks. Hence, the need of securing OMNs arises that becomes important yet a difficult task. Especially, when the OMNs are used for data exchange between end-users, satellites, or the scenarios with matter of urgency such as communication between disaster response teams. This project, helps in identifying attacks in OMNs, studying their impacts, and proposing a detection as well as mitigation schemes.
Collaborations
Target Government Bodies/Industries
E-government and e-commerce are widely implemented in various federal and local government units in UAE. Recent studies showed that the number of computer attacks increased exponentially. The center is keen to reach out all various governmental and industrial institutions to help them to protect their intellectual properties.
The following is a partial list of governmental institutions that the center can start collaborating with:
- Sharjah Electricity and Water Authority (SEWA)
- Dubai Electricity and Water Authority (DEWA)
- Federal Electricity and Water Authority (FEWA)
- Sharjah Police
- Abu Dhabi Police
- Dubai Police
External Organizations
- New York University in Abu Dhabi (Prof. Nasir Memon)
- UAE University, Al Ain (Dr. Ezedin Barka)
- SKOLTECH
- Prof. Ibrahim Kamel, Prof. Tamer Rabie: Protecting copyrights of deep neural networks via digital watermarking)
- Prof. Zaher Al Aghbari: Lightweight DL Models for Data-Intensive IoT applications
Research Publications
No Record Found
Goals and Objectives
Current Research Projects:
- Portable Intelligent Edge Computing Oral Health System based on Deep Learning and IoT technologies.
- Development of an artificial intelligence object detection solution for automatic real-time visual inspection and charting of dental conditions.
- Potential of Artificial Intelligence and Machine Learning algorithms for identification of novel diagnostic biomarkers for early-stage Hepatocellular carcinoma.
- Health Monitoring in Camels Using Computer Vision and Machine Learning.
- Performance Analysis of the Ethereum and Cardano Blockchains.
- A Unified Blockchain-Based Electronic Dental Record (EDR) Ecosystem for Secure Data Exchange.
- FOREX Intelligent RPA.
- Drone Forensic.
- Blockchain Framework for Arabic and Islamic Culture using Metaverse.
- Robust Framework for Aircraft Detection and Type Recognition in Remote Sensing Images.
- Utilization of Heterogeneous Datasets in Developing Federated Learning-Based Intrusion Detection
System.
Past Research Projects:
- Awareness of cybercrimes Among Youth in the UAE Society.
- Blockchain Networks for Solar PV Electric Vehicles Charging Station to Support and Foster Clean Energy Transition.
- Wearable Biosensors Intelligent System for Early Detection of COVID-19 using Data Science Techniques.
- Locational Management for Healthcare Facilities during COVID-19 Pandemic: An Artificial Intelligence Approach.
- Breast Cancer Detection Using Statistical and Deep Learning Techniques.
- Data-Driven False Data Injection Attacks Detection in Smart Grid using state estimation.
- Blockchain Networks for Building Integrated Microgrids and Solar PV Electric Vehicles Charging Station to Support and Foster Clean Energy Transition.
- A Comprehensive Disaster Management Framework for Smart Cities
- Design and Implement Inter Blockchain Communication between Heterogeneous Blockchain Networks.
- Remote Attestation of Cyber Physical Systems (CPS).
- Open Source Software Use for Law Enforcement in the UAE
- Open Source for Education
- IoT Testbed
- Blockchain Performance Evaluation
- Program-Flow Attestation of an IoT Application Software
- Blockchain Information Security Assurance Framework for Smart Government
- Internet of Things (IoT) Information Quality Framework for Transportation System


